Transportation Sector Not Taking Cyber Threat Seriously Enough
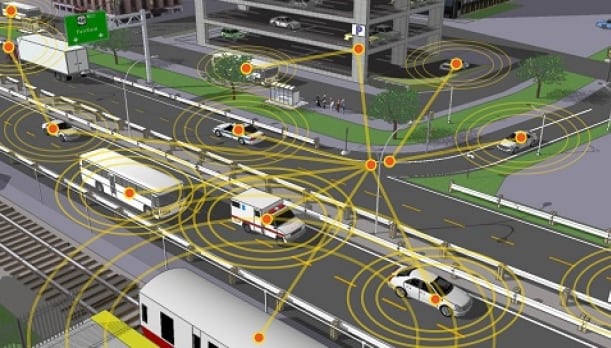
Rendition of connected transportation. Photo: U.S. Department of Transportation.
While transportation cybersecurity spending is expected to increase from $8 billion currently to around $14 billion by 2022, according to ABI Research, the industry could still be vulnerable. Michela Menting, digital security research director at ABI Research, told Via Satellite that this market has picked up over the last few years thanks to smart airports, e-enabled aircraft, automated/driverless trains, connected vehicles, and self-driving cars. This means the development of operational technologies has been much faster than it has been in the past. She believes it is only now that the effect of digitization is being felt within the transportation sector.
But according to ABI Research’s “Critical Infrastructure Security: Transport” report, this rapid digitization is presenting huge problems. Menting believes there is very poor cybersecurity being applied or implemented within transportation operational technologies and control systems. She said this includes critical functionalities such as engine and flight control, electronic positioning systems, chart displays, and navigation systems within aircraft and ships. For example, Menting highlighted the fact that many of these systems now use commercial off-the-shelf software and are internet connected through Wi-Fi and cellular networks.
“The infrastructure operators are not implementing the appropriate cybersecurity mechanisms in these control features as they would in an IT environment. They are simply not familiar enough with cybersecurity in control systems and that is a huge problem, because as they implement these connected technologies, they are ignoring the huge risks that are being introduced into these operational technologies,” said Menting.
The warning is stark. With satellite companies already well entrenched in terms of connected aircraft and ships, as well as developing plans to play in the budding connected car sector, cyber attacks involving transport companies could clearly have an impact on their business.
Menting conceded that the communications systems are definitely “highly vulnerable” and that this includes the satellite channel. She said the use of protocols and networks commonly used in IT systems is widespread, from LAN to cellular. While the use of 5G is being actively debated, 3G/4G is already in widespread use. “In addition, there is high usage of short-range connectivity like Wi-Fi, RFID, and Bluetooth and other proprietary IoT protocols such as Zigbee, 6LowPAN, etc. Satellite communications have been the traditional channel for maritime vessels and aircraft, at least for navigation and guidance, and more recently for infotainment, [high speed data communications for passengers and crew],” she said.
Menting points out that security has been less of a concern for this medium. She believes the more pressing risk is really at the end points where the communications start and end. Those end points are now connected to other systems in the craft/vessel or at the terminals/ports that are digitized and have an IP address. Insecure endpoints are a potential threat vector that can make use of the satellite communications channel to potentially transmit erroneous or malicious data, she says.
With connected transportation becoming more of a reality, the threats to this sector are on the rise. When asked what role the satellite industry will play as this sector starts to develop, Menting pointed to aviation and maritime, and said it will also have an increasing role when it comes to the connected car.
For cars, she believes satellite will be used increasingly beyond simply navigation and said that to see the successful implementation of driverless cars, there must be a secure connectivity element. This includes the short-range connectivity to roadside units, and connecting to the wider infrastructure will require expanded satellite services. There is currently a debate on whether 5G is going to be that next communications channel, rather than Dedicated Short Range Communications (DSRC). Menting believes this will lead to an opportunity for satellite operators to provide that secure connectivity element, including critical updates and real-time information about the roadside traffic.
“On a larger scale going forward, new connectivity requirements will emerge beyond traffic-related services and connect around smart city and smart home elements. I think there is a role for satellite operators there. Cybersecurity adoption in the transport sector is still very nascent and immature. There is plenty of scope for satellite players to extend their role within the secure communications element,” she added.
So, while that is the good news, the connected transportation market seems more vulnerable than others to a crippling cyber attack. Menting said if you look at cyber attacks within the transportation sector, the issues have been around human error and accidental misuses of systems, and that so far, we have not really seen a fully fledged cyber attack. But just because it hasn’t happened yet doesn’t mean there are not warning signs.
“We have had some cybercriminal enterprises ongoing, although most of it specifically targeted rather than large scale indiscriminate cyberattacks — although the latest bout of ransomware is revealing vulnerabilities in the transport infrastructure,” said Menting. “In the maritime sector, organized crime groups have been hacking cargo management systems to check if shipping containers have been flagged as suspicious by border control, or to fake delivery data to allow criminals to obtain delivery of valuable containers. There are also instances of ships falsifying automatic identification system’s data in an attempt to avoid boarding and inspection of containers.”
Menting cited a recent event involving British Airways as an example of the damage that could be done. The grounding of the airline’s flights due to a power outage could be seen as a wake-up call as to how a cyber attack could cripple the business. “There is a negative perception of cost, and a low perception of risk. If the risk is not perceived as dangerous enough or real enough, operators are not going to implement really comprehensive security. They will do the bare minimum. But the transport industry is part of the critical infrastructure, so they should really think about it differently,” commented Menting.
However, it appears the risks are not being taken seriously enough. “The problem with connected digital systems is that a threat actor just needs to find the weakest link. They can easily get into a critical system by penetrating a weaker, or more vulnerable adjacent connected system. The transport sector hasn’t really made the effort to research and assess those types of risks fully. They understand the IT risks, but they have not done that full risk assessment on the operational side,” added Menting.