Blogtrepreneur.
IOActive’s process of reverse engineering satellite communications products has unveiled a range of potential vulnerabilities that have become commonplace across maritime connectivity. The security consultancy’s discoveries contributed to Inmarsat discontinuing its AmosConnect 8 platform in June, and in a recent blog post, principal advisor Mario Ballano laid out the technical details of the weaknesses they found.
According to Ballano, in order to reverse-engineer satcom products, IOActive consultants will crack open a piece of hardware and extract its firmware. In the case of AmosConnect, the firmware was publicly available to download on Inmarsat’s website. That in itself is problematic, he said in an interview with Via Satellite, because malicious actors with easy access to such information can perform the same reverse engineering process to uncover exploitable weaknesses.
“We basically use disassemblers, decompilers and a number of different tools to analyze the binary code and try to understand exactly how the program works. By doing that you may be able to uncover security issues among other things,” Ballano said.
According to Ballano, the security flaws evident in AmosConnect 8 — a platform that provided email, instant messaging, position reporting and more — were two-fold. The first lapse was its vulnerability to a blind Structured Query Language (SQL) injection, an attack that could have allowed hackers to gain access to credentials the platform stored in its database. Because the server stored usernames and passwords in plain text, this vulnerability was “trivial to exploit,” Ballano said.
The AmosConnect 8 server also hosted a “backdoor” account with full system privileges. With just a few commands, IOActive was able to show that attackers could obtain administrator credentials to log into the platform’s portal, giving them free reign to access the server by burrowing through the IT systems network, for example.
Other than basic firewalls, Ballano noted that important cybersecurity measures are absent in many satcom products because it is assumed they will be physically inaccessible to hackers. “We have found significant vulnerabilities across different elements of satellite networks,” he said. “Maybe the reason for that is because these environments are usually isolated. You have some equipment that is sitting on a vessel or software that can only be accessed by crew members, so security was often overlooked.”
[contextly_sidebar id=”sxjICppkfvysOO9yRPCNjqAkSdFSvkPl”]Inmarsat’s response, released just after the IOActive report went public, seemed to echo this sentiment: “It is important to note that this vulnerability would have been very difficult to exploit as it would require direct access to the shipboard PC that ran the AC8 email client. This could only be done by direct physical access to the PC, which would require an intruder to gain access to the ship and then to the computer. While remote access was deemed to be a remote possibility as this would have been blocked by Inmarsat’s shoreside firewalls,” the company stated.
Had the vulnerability in AmosConnect’s system been exploited, a savvy hacker could have gotten hold of sensitive corporate data or access any other resources present in the server, Ballano said.
According to a 2014 IOActive white paper, the weaknesses it found in AmosConnect 8 and other similar security flaws are present in multiple satcom products across the market. “It seems there might be quite a number of devices and software being used in this environment that would be vulnerable to attacks like the ones we have described in our research,” Ballano said.
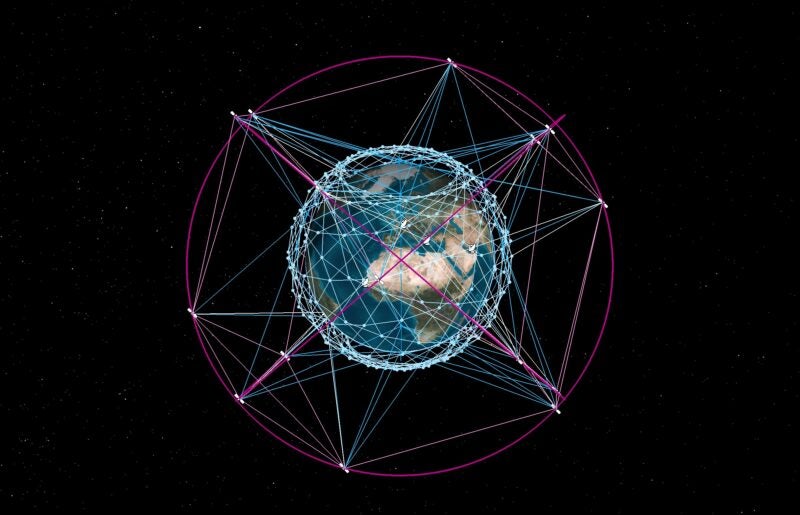
“Some of the flaws we identified include the use of unencrypted signaling protocols that could be abused by an attacker to track who is connecting to a satellite and how the satellite network is being used in real time,” he added. “Our research has shown that poor configuration of the satellite infrastructure network can often allow attackers to access important nodes within the network and even other customers’ satellite terminals.”
In a world where analysts can reverse engineer a piece of hardware or software to understand its secrets, proprietary protocols simply aren’t enough to ensure satellite infrastructure is secure. Ballano suggested satcom product providers work with third parties to test the security of their satellite networks as a whole, ranging from the network configuration to the security of satellite terminals.
“Have a proactive vision into the security of your environment,” he said.