DOD Heightens Importance of Cybersecurity in Future Ground Systems
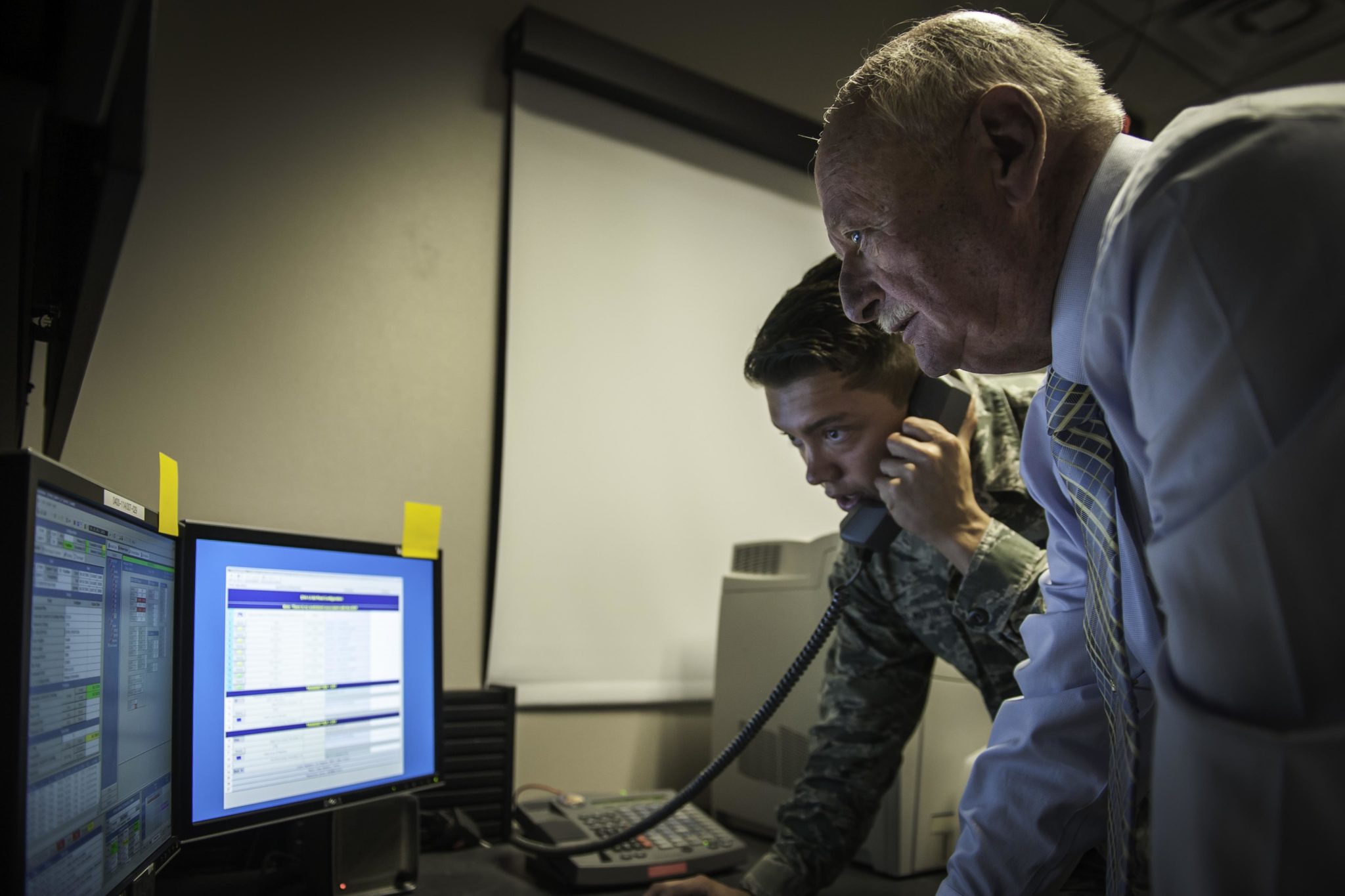
Contractor Jim Brewer and Senior Airman Guillermo Delacruz-Martinez, 2nd Space Operations Squadron, send the disposal command to GPS Satellite Vehicle No. 35 at Schriever Air Force Base, Colorado, Friday, June 10, 2016. The command marked the vehicle’s end of life. Photo: U.S. Air Force/Dennis Rogers
[Via Satellite 09-22-2016] The U.S. Department of Defense (DOD) wants to make sure its future ground system for government satellites, known as the Enterprise Ground Segment (EGS), makes cybersecurity a much bigger priority compared to the approach taken with ground systems currently in use. Today, DOD ground systems for military satellite programs all run separate from each other. EGS will seek to unify ground segment operations onto a single comprehensive system, but DOD does not want to make that system into a jackpot hack for intruders who could see it as an opportunity to get into every military satellite system at once.
Speaking Sept. 22 at a Mitchell Institute event, Colonel Brian Bracey, chief architect at the Advanced Systems and Development Directorate of Air Force Space Command (AFSPC), said all of today’s DOD programs of record have the same problems in regard to cyber, and that the current defense strategy relies heavily on what DOD perceives to be the system’s greatness weakness: dissimilarity.
“The best term I’ve heard right now, is that right now we have resilience through diversity, which means that everyone of the systems is different, but every one of those is exposed,” he said.
The military desires to move away from siloed, or “stovepiped” ground segments for different satellite systems, finding this approach to be costly and cumbersome. The goal of EGS is to unite these disparate operations into one single system. DOD is aware, however, of the lure that could create for potential hackers.
“If you aggregate all the satellites onto one network, you just created a great big target,” said Colonel John Anttonen, director of the Advanced Systems and Development Directorate and commander of Space and Missile Systems Center (SMC) Detachment 1. “So what are you going to do about it? When we look at cyber defense and the way we approach those today, we have to change what we do.”
Bracey said DOD wants to reduce the “cyber surface attack area” of military ground systems to reduce the number of vulnerabilities intruders could exploit. DOD ground systems are exposed through “a tremendous number of attack vector points,” Bracey said, because different systems each have different characteristics, contractors and personnel to operate them. As a result, the entire system gets too unwieldy to effectively protect.
“Right now we don’t know what we’re not defending because there are so many different things that are out, and we don’t have the manpower and the tools to put across there,” he said.
Furthermore, Bracey said the sustainment costs of operating separate systems are getting difficult for DOD to afford. With GPS, for example, he said there is the potential risk of having four separate ground infrastructures at Schriever Air Force Base, because DOD does not scrap legacy gear until it is fully confirmed that new systems will work. GPS already has two different ground systems, and because of the high-profile delays with implementing Raytheon’s next generation Operational Control System (OCX), there is an interim solution as well.
“That’s four different sets of racks, that’s four different sets of contracts in some cases, that’s four different sets of system administrators, that’s [Heating, Ventilation, and Air Conditioning] HVAC, power, floor space, and that’s training plans for each one of those operators … that is a tremendous consumption of manpower at the 50th Space Wing,” said Bracey.
Bracey added that reducing the number of cyber surface attack areas does not guarantee complete protection, but it does reduce the number of places that require monitoring. By reining in this number, he said cybersecurity experts could devote their focus on the most probable points of attack, and be better able to locate the origin if something happens.
To reach this heightened level of cybersecurity, Anttonen said SMC is taking a different approach than it has on other space programs. While SMC wants lots of involvement from industry throughout EGS, with cybersecurity, specialists are preferred.
“We are not trying to tie cyber defense into the folks that are delivering the spacecraft. We would really rather it be tied to folks that their business is cyber defense. Using companies and using systems that are already being developed to defend the nation’s networks today is what we are interested in,” he said, stressing the importance of leveraging the strengths of different companies to make EGS strong, whether that strength is with satellites, designing networks, collecting data, cybersecurity, or something else.